Zero Trust Architecture for the CAS-005 Exam: Microsegmentation, SASE, and SD-WAN Explained
Zero trust architecture CAS-005 knowledge is no longer optional for senior security engineers and architects. CompTIA CASP+ CAS-005 expects you to move beyond buzzwords and design concrete architectures that apply zero trust principles across on-prem, cloud, and remote access.
This tutorial connects NIST SP 800-207 Zero Trust Architecture (ZTA) to the CompTIA CASP+ CAS-005 exam. You will see how microsegmentation, SASE, and SD-WAN implement zero trust in real networks and how to reason through exam-style scenarios and PBQs.
The audience here is an experienced defender or architect. We will keep the theory tight, focus on design trade-offs, and constantly tie decisions back to the CAS-005 blueprint.
TL;DR: Zero Trust for CAS-005 in One Page
Zero trust is an architecture pattern, not a single product. NIST SP 800-207 frames it around continuous verification, least privilege, and assuming breach.
For CAS-005 you should be able to:
- Explain the core zero trust principles and the NIST PDP/PEP model.
- Design microsegmentation strategies that contain lateral movement.
- Compare SASE vs. SD-WAN and when to use each in deperimeterized architectures.
- Map identity, device posture, and context signals into policy for exam scenarios.
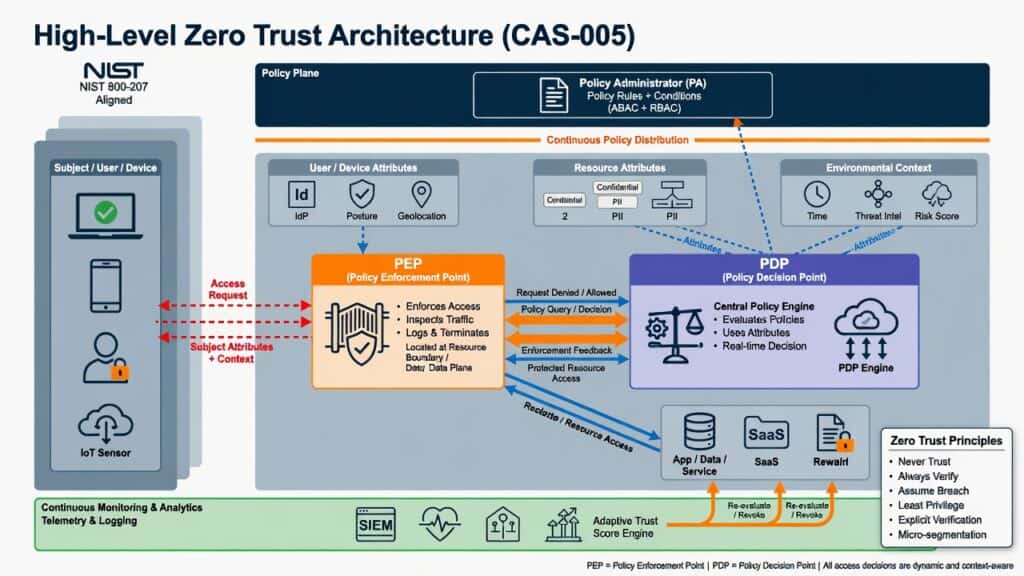
1. Zero Trust Architecture: What NIST 800-207 Actually Says
NIST SP 800-207 gives a widely referenced definition of zero trust architecture. CAS-005 does not expect you to quote the document, but it does expect you to design systems that follow its principles.
At its core, NIST ZTA is built on these ideas:
- Never trust, always verify – every access request is evaluated as if it came from an untrusted network.
- Assume breach – design controls assuming an attacker is already inside some part of the environment.
- Least privilege and just-in-time access – grant only the minimum required access, for the shortest time needed.
- Continuous evaluation – access is not “one and done”; posture and context are checked throughout the session.
NIST models ZTA around two main logical components:
- Policy Decision Point (PDP) – where the access decision is made. It uses policies, identity, device posture, threat intel, and context.
- Policy Enforcement Point (PEP) – where traffic is allowed, blocked, or shaped based on the PDP’s decision.
In real deployments, the PDP might be a centralized policy engine, while PEPs live in:
- NGFWs and secure web gateways
- SD-WAN edge devices
- Identity-aware proxies and ZTNA/SASE points of presence
- Host-based agents enforcing microsegmentation policies
CAS-005 angle: in design questions, identify which components act as PDP vs. PEP and evaluate whether the policy signals are rich enough (identity, device, context) to support zero trust decisions.
2. Where Zero Trust Appears in the CAS-005 Blueprint
CompTIA’s official CASP+ CAS-005 objectives emphasize advanced security architecture, deperimeterization, and design topics where zero trust concepts are highly applicable. Zero trust also shows up implicitly in:
- Identity-centric security and zero trust network access (ZTNA)
- Secure remote access patterns for hybrid work
- Cloud and SaaS shared responsibility and access models
- Network segmentation, microsegmentation, and SDN
- SASE and SD-WAN under deperimeterization and architecture topics
On the exam, zero trust is rarely labeled as a pure definition question. Instead, it appears as:
- PBQs where you must place controls, choose technologies, and justify design decisions.
- Scenario MCQs that ask for the “best” architecture to meet business, security, and compliance requirements.
- Trade-off questions (e.g., performance vs. inspection depth, user experience vs. security posture).
Think of zero trust as the design lens you apply when answering architecture questions, especially anything involving remote workers, multi-cloud, and third-party access.
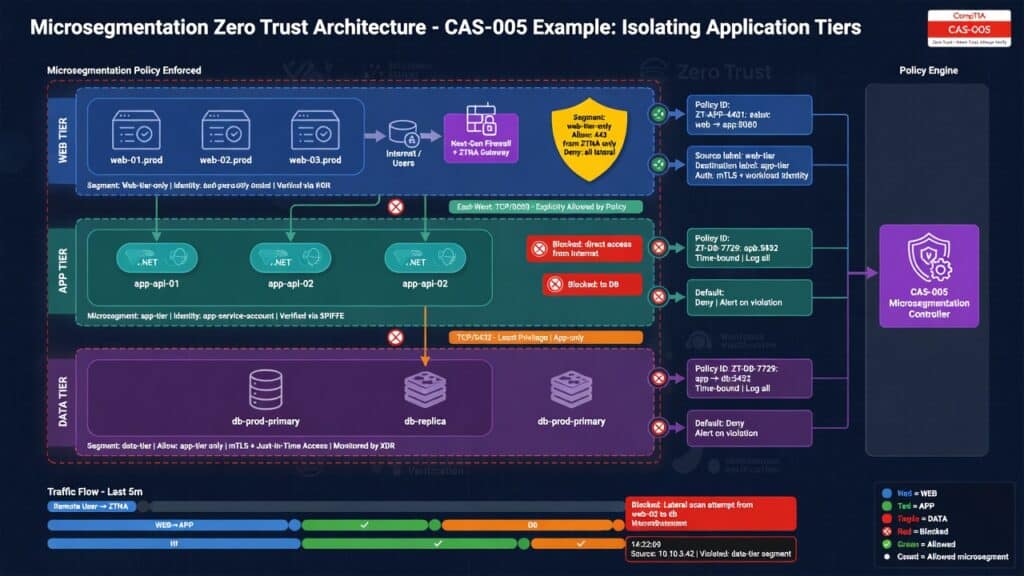
3. Microsegmentation: Containing Lateral Movement
Microsegmentation takes traditional network segmentation down to a much finer level. Instead of a few VLANs or zones, you define granular policies between workloads, applications, or even processes.
3.1 Microsegmentation in a Zero Trust World
Microsegmentation directly supports the zero trust principle of minimizing implicit trust. Even if an attacker compromises one workload, microsegmentation policies prevent easy lateral movement to others.
You will see it implemented as:
- Host-based firewalls or agents that enforce per-workload policies.
- SDN policies in virtualized environments (e.g., hypervisor-level enforcement).
- Container network policies in Kubernetes and similar platforms.
In NIST ZTA terms, the policy engine (PDP) uses identity, labels, and context to generate rules that PEPs enforce at the host or virtual switch layer.
3.2 Microsegmentation Design Patterns for CAS-005
Expect CAS-005 to give you a scenario such as “protect a crown-jewel application in a hybrid data center.” A zero trust–aligned microsegmentation design might:
- Place the application tiers (web, app, DB) into separate segments or security groups.
- Use identity- or label-based policies (e.g., “web-tier can talk to app-tier on port 443 only”).
- Require mutual TLS between services with certificate-based identity.
- Enforce host-based firewall rules that allow only expected east–west flows.
From an exam perspective, compare answers that:
- Reduce the attack surface (fewer open ports, explicit allow rules).
- Support fine-grained policy at the workload level, not only at the perimeter.
- Integrate with central policy orchestration (aligns to PDP/PEP model).
3.3 Microsegmentation Pitfalls and Exam Traps
Common traps in CAS-005 options around microsegmentation include:
- “Flat VLANs with ACLs at the core” – this is traditional segmentation, not microsegmentation.
- “Single shared management network for all servers” – creates a lateral movement highway.
- “Rely only on IP ranges for policy” – ignores identity and labels, less adaptive in cloud.
- “Open all east–west traffic, inspect only north–south” – contradicts zero trust assumptions.
Choose designs that segment critical assets, avoid shared trust zones, and can adapt as workloads move between on-prem and cloud.
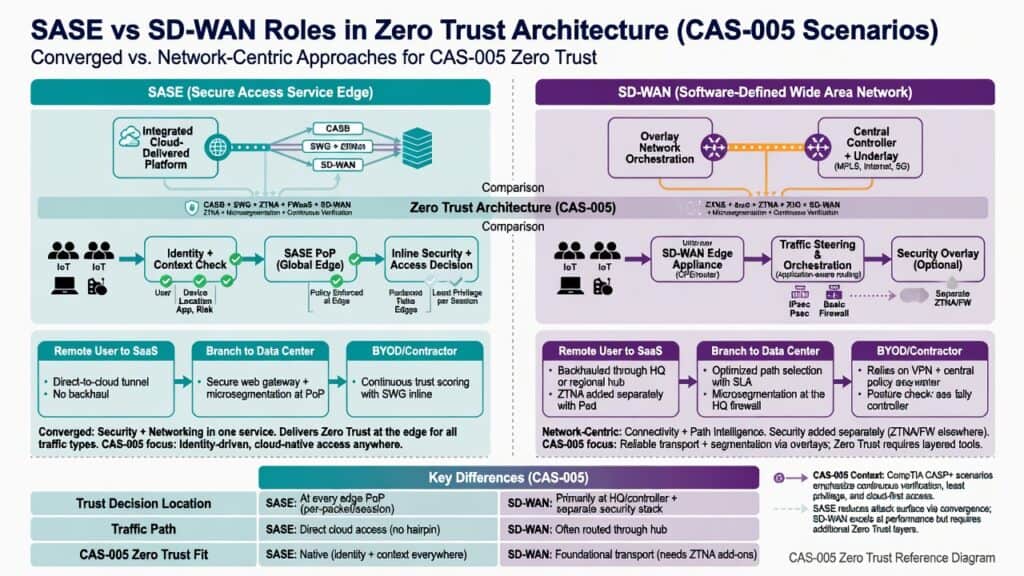
4. SASE: Zero Trust for a Deperimeterized Workforce
Secure Access Service Edge (SASE) combines networking and security functions into a cloud-delivered service. It is central to CAS-005 topics around deperimeterization, SASE, SD-WAN, and software-defined networking.
Most SASE offerings converge:
- SD-WAN capabilities (intelligent path selection, traffic steering).
- Security services like secure web gateway, CASB, firewall-as-a-service, and ZTNA.
- Identity-centric controls using SSO, MFA, device posture, and user context.
4.1 How SASE Implements Zero Trust
SASE is a natural fit for NIST ZTA:
- The SASE cloud edge acts as a distributed PEP, enforcing zero trust policies close to the user.
- Central policy engines, integrated with identity providers (IdPs), act as the PDP.
- Policies consider user identity, device posture, location, application sensitivity, and risk signals.
Instead of backhauling all traffic to a central data center, users connect to the nearest SASE PoP, which then applies security and routes traffic optimally.
4.2 SASE Design Decisions for CAS-005 Scenarios
Typical CAS-005 scenarios where SASE is the right answer:
- A global organization with remote and hybrid workers accessing SaaS and IaaS.
- Need to apply consistent security policies regardless of user location.
- Desire to simplify branch appliances by moving security functions to the cloud.
In such questions, look for solutions that:
- Integrate identity-aware access (SSO, MFA, conditional access).
- Provide application-level visibility and control (not just IP/port).
- Offer direct-to-cloud paths with in-line inspection to reduce latency.
SASE is especially aligned with zero trust network access (ZTNA), where users are granted access to specific applications, not the entire network.
4.3 Avoiding SASE Exam Gotchas
Beware of answer choices that mix old and new patterns in confusing ways. Common traps:
- “Full-tunnel VPN to HQ for all traffic” – high latency for SaaS, not aligned with SASE.
- “Site-to-site VPN only, no identity awareness” – network-centric, not user-centric.
- “Split tunneling with no cloud security stack” – may expose unmanaged traffic.
When the requirements emphasize global scale, cloud adoption, and user-centric policy, SASE/ZTNA solutions usually align better with zero trust than legacy VPN designs.
5. SD-WAN: Secure, Intelligent Connectivity for Zero Trust
SD-WAN is a software-defined approach to WAN connectivity that dynamically steers traffic across multiple links (MPLS, broadband, LTE, etc.). CAS-005 places SD-WAN alongside SASE and SDN in discussions of modern, deperimeterized architectures.
On its own, SD-WAN is primarily about performance, reliability, and cost optimization. But in a zero trust architecture, SD-WAN edges often act as:
- PEPs enforcing security and segmentation policies at branch sites.
- On-ramps to SASE clouds or central security stacks.
- Enforcers of application-aware routing based on identity and risk.
5.1 SD-WAN vs. SASE in Exam Questions
CAS-005 may present both SD-WAN and SASE as options. Distinguish them like this:
- SD-WAN-centric design – focus on branch-to-HQ or branch-to-cloud connectivity, link optimization, and local enforcement.
- SASE-centric design – focus on user-to-application access, identity-based zero trust controls, and cloud-delivered security.
Modern architectures often combine them: SD-WAN edges connect branches to SASE PoPs, and SASE provides advanced security and ZTNA.
5.2 SD-WAN Security Capabilities Aligned with Zero Trust
When SD-WAN is integrated with security, look for features like:
- Application-aware policies – route and secure traffic based on app identity, not just IP/port.
- Integrated NGFW/IPS – inspection at the branch edge, acting as a PEP.
- Per-application path selection – sensitive apps forced through more secure or inspected paths.
In exam scenarios, SD-WAN is often the right answer when the driver is optimizing multi-link WAN cost and performance while still applying consistent security controls.
6. Putting It Together: A Zero Trust Reference Architecture for CAS-005
Let’s combine these concepts into a high-level architecture you can reuse mentally on the exam.
6.1 Components in the Reference Design
- Identity & Access Management (IAM) – IdP, SSO, MFA, conditional access.
- Device posture – EDR, MDM, compliance checks feeding into policy.
- SASE / ZTNA cloud – global PEPs enforcing user-to-app policies.
- SD-WAN edges – branch connectivity, local PEP for sites.
- Microsegmentation platform – per-workload policies in data centers and clouds.
- Central policy engine (PDP) – consolidates identity, posture, threat intel, and context.
6.2 Example Flow: Remote User to Crown-Jewel App
- User authenticates via SSO + MFA to the IdP.
- Device posture is checked (EDR, OS patch level, encryption status).
- User connects to the nearest SASE PoP, which acts as a PEP.
- SASE consults the PDP: user role, device posture, location, time, and risk.
- If allowed, traffic is sent over an SD-WAN path to the data center or cloud.
- In the data center, microsegmentation allows only required flows to the app and DB tiers.
- Continuous evaluation monitors for anomalies; access can be revoked mid-session.
Every step embodies zero trust: no implicit trust based on network location, continuous verification, and least privilege.
6.3 How to Think Through Similar PBQs
When CAS-005 gives you a design PBQ:
- Identify trust boundaries – users, branches, data centers, clouds, partners.
- Place PEPs at each boundary (SASE PoP, SD-WAN edge, host agent).
- Identify what acts as the PDP – where policies are evaluated.
- Ensure identity, device, and context are part of the decision, not just IP.
- Apply microsegmentation around high-value assets to contain breach impact.
If two options both “work,” choose the one that reduces implicit trust, centralizes policy, and supports continuous verification.
7. Zero Trust Architecture Study Strategy for CAS-005
Zero trust is a high-yield topic because it cuts across multiple domains. A focused study plan will pay off in both PBQs and scenario questions.
7.1 Anchor on NIST SP 800-207
You do not need to memorize the entire document, but you should know:
- The core zero trust principles.
- The PDP/PEP model and related components (policy engine, policy administrator, policy enforcement point).
- That ZTA is agnostic to specific products – focus on patterns, not vendor names.
Skim NIST diagrams and map them to the SASE, SD-WAN, and microsegmentation components you already know.
7.2 Practice Architecture Mapping
Use a few short exercises to reinforce concepts:
- Take your current network and mark where PEPs exist (firewalls, proxies, agents).
- Identify what acts as the PDP (policy servers, IAM, SASE controllers).
- Sketch how you would add microsegmentation around your most critical application.
- Design a SASE/SD-WAN rollout for two branches and remote workers.
These exercises mirror the mental work required to navigate CAS-005 PBQs.
7.3 Connect Zero Trust to Other CAS-005 Topics
Zero trust also ties into:
- Incident response and threat hunting – microsegmentation and PEP logs help detect and contain lateral movement.
- Vulnerability management – segmentation reduces blast radius while you prioritize remediation.
- Third-party risk – ZTNA and SASE help enforce least privilege for vendors and partners.
When studying, consciously frame these topics through a zero trust lens.
8. CAS-005-Style Zero Trust Q&A
Use these questions as quick checks while you revise.
8.1 How does zero trust change remote access design compared to legacy VPNs?
Legacy VPNs often place users on an internal network after authentication, granting broad access based on IP. Zero trust remote access (via ZTNA/SASE) instead:
- Authenticates with SSO + MFA and checks device posture.
- Grants access only to specific applications, not whole subnets.
- Continuously evaluates risk and can revoke access mid-session.
- Applies consistent policy whether the user is on-prem or remote.
8.2 When is microsegmentation a better answer than just “more firewalls”?
Microsegmentation is better when the requirement is to:
- Limit east–west lateral movement inside data centers or clouds.
- Apply per-workload or per-application policies, not just subnet-level rules.
- Support dynamic environments where workloads move or scale frequently.
Adding more perimeter firewalls may improve north–south control but does not address granular internal trust zones.
8.3 How do SASE and SD-WAN complement each other in zero trust?
SD-WAN optimizes connectivity between sites and clouds, while SASE delivers cloud-based security and access control. Together they:
- Use SD-WAN edges to route traffic intelligently to the nearest SASE PoP.
- Let SASE enforce identity- and context-aware policies at the edge.
- Provide resilient, secure access for both branches and remote users.
9. Conclusion: Zero Trust Architecture CAS-005 Takeaways
If you remember one thing for the zero trust architecture CAS-005 portion of your prep, make it this: CompTIA wants you to design systems that minimize implicit trust and assume breach, not just recite definitions.
Microsegmentation, SASE, and SD-WAN are three concrete ways to implement these ideas:
- Microsegmentation contains lateral movement with granular policies.
- SASE brings identity-centric zero trust controls to remote and cloud access.
- SD-WAN provides intelligent, secure connectivity that feeds into your zero trust fabric.
Anchor your thinking in NIST SP 800-207, map exam scenarios to PDP/PEP, and consistently favor architectures that reduce implicit trust. With that mindset, many CAS-005 zero trust questions become straightforward design choices, not guesswork.