TL;DR: A RACI matrix clarifies who is Responsible, Accountable, Consulted, and Informed for cybersecurity tasks. Use it to map roles to key activities like incident response, vulnerability management, and risk assessments so nothing falls through the cracks and you align with SecurityX CAS-005 governance objectives.
RACI Matrix in Cybersecurity: How to Assign Security Roles the Right Way
A RACI matrix in cybersecurity is one of the simplest ways to remove confusion about who does what in your security program. For the SecurityX CAS-005 exam and real-world work, you must understand how to assign security roles clearly and prove accountability.
This tutorial shows you exactly how to build and use a RACI matrix for security operations, incident response, and governance, with examples you can reuse on the job and in your exam prep.
What Is a RACI Matrix in Cybersecurity?
A RACI matrix (Responsibility Assignment Matrix) is a table that shows the level of involvement each role has for a task or deliverable. In cybersecurity, it connects security activities to people and teams so responsibilities are explicit.
RACI stands for:
- R – Responsible: The “doers” who perform the work.
- A – Accountable: The single owner answerable for the outcome.
- C – Consulted: Subject matter experts who provide input.
- I – Informed: Stakeholders kept up to date on progress or results.
For example, in a phishing incident:
- The SOC analyst may be Responsible for triage.
- The Incident Response (IR) manager is Accountable for the overall handling.
- Legal and HR could be Consulted.
- The CISO and business owner are Informed.
SecurityX CAS-005 treats the RACI matrix as a governance and GRC framework tool to support accountability, separation of duties, and effective risk management.
Why RACI Matters for SecurityX CAS-005 and Real Programs
On the exam and in the field, the RACI matrix supports several key cybersecurity objectives.
1. Eliminates Role Confusion During Incidents
During an incident, you do not want people debating who has authority to isolate a system. A documented RACI matrix:
- Pre-defines who can make containment decisions.
- Clarifies who communicates with executives and regulators.
- Reduces delays and conflicting actions.
2. Supports Governance, Risk, and Compliance (GRC)
Regulations and frameworks (ISO 27001, NIST CSF, PCI DSS) expect clear assignment of security roles and responsibilities. A RACI matrix:
- Shows auditors how tasks map to roles.
- Helps demonstrate management commitment and oversight.
- Aligns with SecurityX CAS-005 governance objectives around accountability.
3. Improves Security Operations and Resource Planning
When you map tasks like vulnerability management or threat hunting to roles, you can see where you lack capacity or have single points of failure. This informs hiring, training, and outsourcing decisions.
For CAS-005, be able to explain how a RACI matrix supports security operations, incident response, and risk management processes.
Core RACI Concepts You Must Know for the Exam
Before you build your own RACI matrix for cybersecurity, make sure you understand these exam-relevant details.
Responsible vs. Accountable in a Security Context
This distinction is a common exam trap:
- Responsible (R): Executes the task. There can be multiple Rs.
- Accountable (A): Owns the task and is answerable for success or failure. There should be only one A per task.
On SecurityX-style questions, if you see “who is ultimately answerable for the control’s effectiveness,” the answer is the Accountable role, not the Responsible one.
Consulted and Informed Roles
In cybersecurity, Consulted and Informed roles often include:
- Consulted: Legal, HR, Privacy officers, Data owners, Enterprise architects.
- Informed: Executives, business unit leaders, end users, regulators (through formal reporting).
For exam scenarios, think about who must give input before action (Consulted) and who only needs status updates (Informed).
Typical Cybersecurity Roles in a RACI Matrix
Your RACI matrix can include technical and non-technical roles, such as:
- CISO / Director of Security
- Security Architect
- Security Engineer
- SOC Analyst / Threat Hunter
- Incident Response Manager
- IT Operations / System Administrators
- Risk Manager / GRC Analyst
- Data Owner / Business Owner
- Legal and HR
You may also include external roles like managed security service providers (MSSPs) or cloud providers, especially for third-party risk questions.
How to Build a Cybersecurity RACI Matrix in 5 Steps
Use this step-by-step approach to create a practical RACI matrix that you can adapt to your environment and map back to SecurityX CAS-005 objectives.
Step 1: Identify Key Security Processes
Start by listing the core security processes or tasks you want to control. Typical candidates include:
- Security policy development and review
- Risk assessment and risk register maintenance
- Vulnerability scanning and patch management
- Security monitoring and log review (SIEM)
- Incident detection, triage, containment, eradication, and recovery
- User access reviews and identity lifecycle management
- Security awareness training
- Third-party risk assessments
For exam alignment, think of the entire security lifecycle: governance, prevention, detection, response, and recovery.
Step 2: List Roles, Not Individual Names
Next, list the roles across the top of your matrix. Avoid personal names so the RACI remains valid even if staff change. For example:
- CISO
- Security Architect
- SOC Lead
- SOC Analyst
- Incident Response Manager
- IT Operations Lead
- Risk Manager
- Data Owner
- Legal Counsel
On the exam, roles are usually presented at this level of abstraction.
Step 3: Assign R, A, C, and I for Each Task
Now, for each task, decide which role is Responsible, which is Accountable, and who is Consulted or Informed.
Simple rules:
- Each task should have at least one Responsible.
- Each task should have exactly one Accountable.
- Consulted and Informed are optional but recommended for clarity.
Think in terms of authority and expertise. Who can approve? Who has the skills to execute? Who will be impacted by the outcome?
Step 4: Validate with Stakeholders
Walk through the draft matrix with key stakeholders (security leadership, IT, business owners). Confirm that:
- They understand and accept their roles.
- There are no overlapping “A” assignments that cause conflict.
- Critical activities are not missing an R or A.
This step is essential for real programs, and it reflects the management commitment and communication aspects tested in SecurityX CAS-005.
Step 5: Integrate with Playbooks and Governance Documents
Finally, embed your RACI matrix into:
- Incident response playbooks
- Change management procedures
- Risk management and compliance processes
- Security policy and standard documents
This ensures the RACI is not just a slide but a living part of your security governance framework.
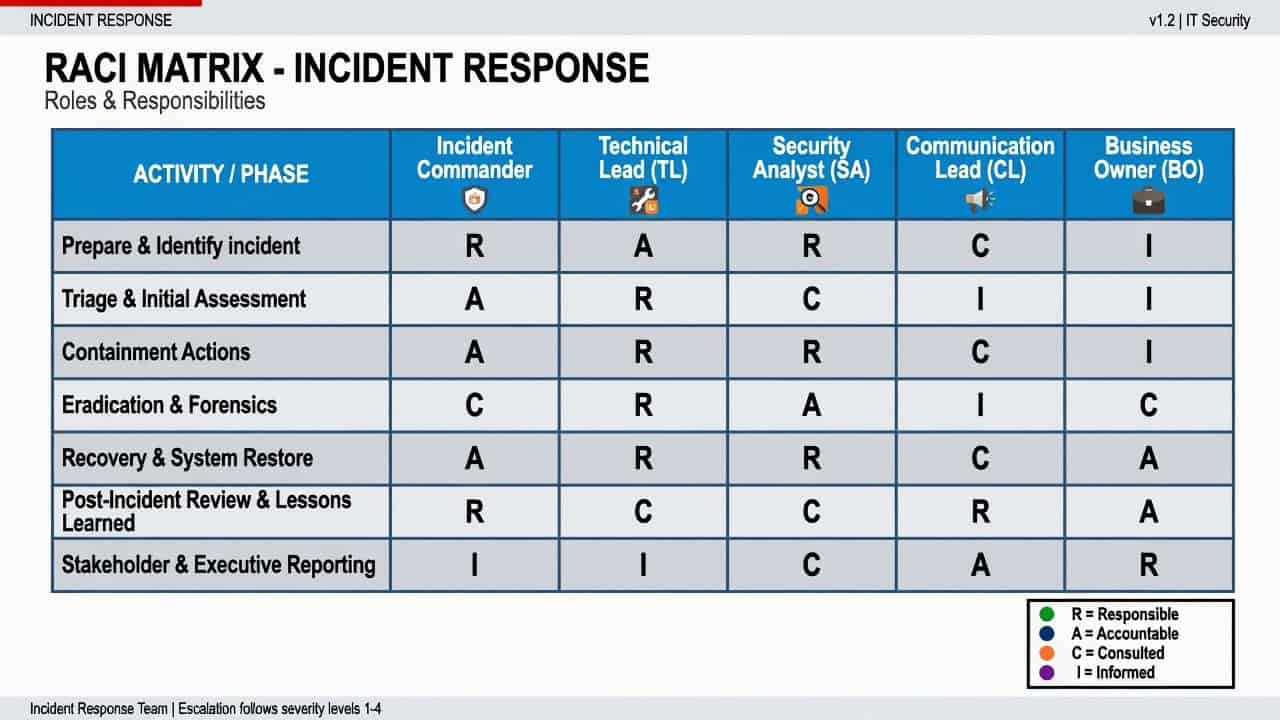
Example: RACI Matrix for Incident Response
Here is a simplified example of a RACI matrix in cybersecurity focused on incident response. Roles:
- CISO
- Incident Response (IR) Manager
- SOC Analyst
- IT Operations
- Legal
- Business Owner
Key tasks and RACI assignments:
| Task | CISO | IR Manager | SOC Analyst | IT Ops | Legal | Business Owner |
|---|---|---|---|---|---|---|
| Detect and log security events | I | C | R / A | I | I | I |
| Classify incident severity | I | A | R | C | C | C |
| Contain affected systems | I | A | R | R | I | I |
| Eradicate root cause | I | A | R | R | I | I |
| Communicate major incident to executives | A | R | I | I | C | I |
| Regulatory / legal notifications | I | C | I | I | A / R | C |
| Post-incident review | A | R | R | R | C | C |
This example highlights two important patterns:
- The IR Manager is often Accountable for incident handling.
- Legal is Accountable for regulatory notifications, with security and business as Consulted.
On the exam, you may see scenario questions where you must infer which role is Accountable versus Responsible for activities like notification, communication, or remediation.
Tips for Using RACI in SecurityX CAS-005 Exam Questions
Here are practical strategies to handle RACI-related questions in SecurityX CAS-005.
Map the Action Verb to the RACI Role
Look for key verbs in the question stem:
- “Execute,” “perform,” “implement” → Responsible
- “Own,” “approve,” “sign off” → Accountable
- “Provide input,” “advise,” “review” → Consulted
- “Be notified,” “receive updates” → Informed
This mapping can help you eliminate distractors quickly.
Think in Terms of Governance Layers
In governance questions:
- Business leadership (CIO, CISO, board) are often Accountable for policy and risk acceptance.
- Security and IT staff are typically Responsible for implementing controls.
- Risk and compliance teams are Consulted on control design and assessment.
- Business units are Informed or Consulted depending on impact.
Use these patterns when you see ambiguous answer choices.
Watch Out for Multiple “A” Assignments
If an answer option assigns multiple Accountable roles for a single task, that is usually a red flag. Proper RACI design avoids shared accountability for the same activity.
Common Pitfalls When Implementing a Cybersecurity RACI Matrix
Whether in exam scenarios or your own organization, be aware of these RACI pitfalls.
Overloading the Security Team
Many organizations assign security as both Responsible and Accountable for almost everything. This can:
- Hide business ownership of risk.
- Overwhelm security staff.
- Contradict governance principles where the business owns risk decisions.
Instead, make business owners Accountable for risk acceptance, with security Responsible for implementing and advising.
Ignoring Third-Party and Cloud Responsibilities
Cloud and SaaS services introduce shared responsibility. Your RACI matrix should:
- Clarify what the provider secures (e.g., underlying infrastructure).
- Clarify what your team secures (e.g., data, identities, configurations).
- Assign roles for managing vendor risk assessments and SLAs.
SecurityX CAS-005 often tests awareness of shared responsibility models and third-party risk management.
Letting the RACI Matrix Go Stale
Roles, tools, and processes change. Review your RACI at least annually or after major events such as:
- Organizational restructuring
- New regulations or compliance requirements
- Adoption of new cloud platforms or critical applications
- Significant security incidents
This aligns with continuous improvement and security program management expectations on the exam.
How to Practice RACI Skills for SecurityX CAS-005
To make RACI second nature before your exam:
- Redraw the example incident response RACI from this article by hand.
- Create a mini RACI for vulnerability management in your own environment.
- Take a sample PBQ (performance-based question) and annotate which roles are R, A, C, and I for each step.
- Discuss RACI with your team and compare interpretations of who owns which tasks.
This not only prepares you for CAS-005 questions but also improves your day-to-day effectiveness as a security leader or architect.
Conclusion: Make the RACI Matrix a Core Security Tool
A well-designed RACI matrix in cybersecurity turns vague expectations into clear, actionable responsibilities. It supports governance, speeds up incident response, and aligns with SecurityX CAS-005 objectives around accountability and risk ownership.
Start with a small scope—such as incident response or vulnerability management—then expand your RACI across the security program. The more you use RACI thinking in your daily work, the easier related exam questions will feel.
Next, pair your RACI matrix with strong incident playbooks and a formal risk management process to build a mature, exam-ready security program foundation.