Threat Modeling with MITRE ATT&CK, STRIDE, and the Diamond Model: A CAS-005 Study Guide
Threat modeling is a core skill for senior security architects and analysts, and it appears across multiple CompTIA CASP+ CAS-005 domains, including Enterprise Security Architecture, Enterprise Security Operations, and Governance, Risk, and Compliance (GRC).[1][2] For CAS-005, you’re expected to reason about attacker behavior, system design, and compensating controls in complex, hybrid environments—not just memorize definitions.[2]
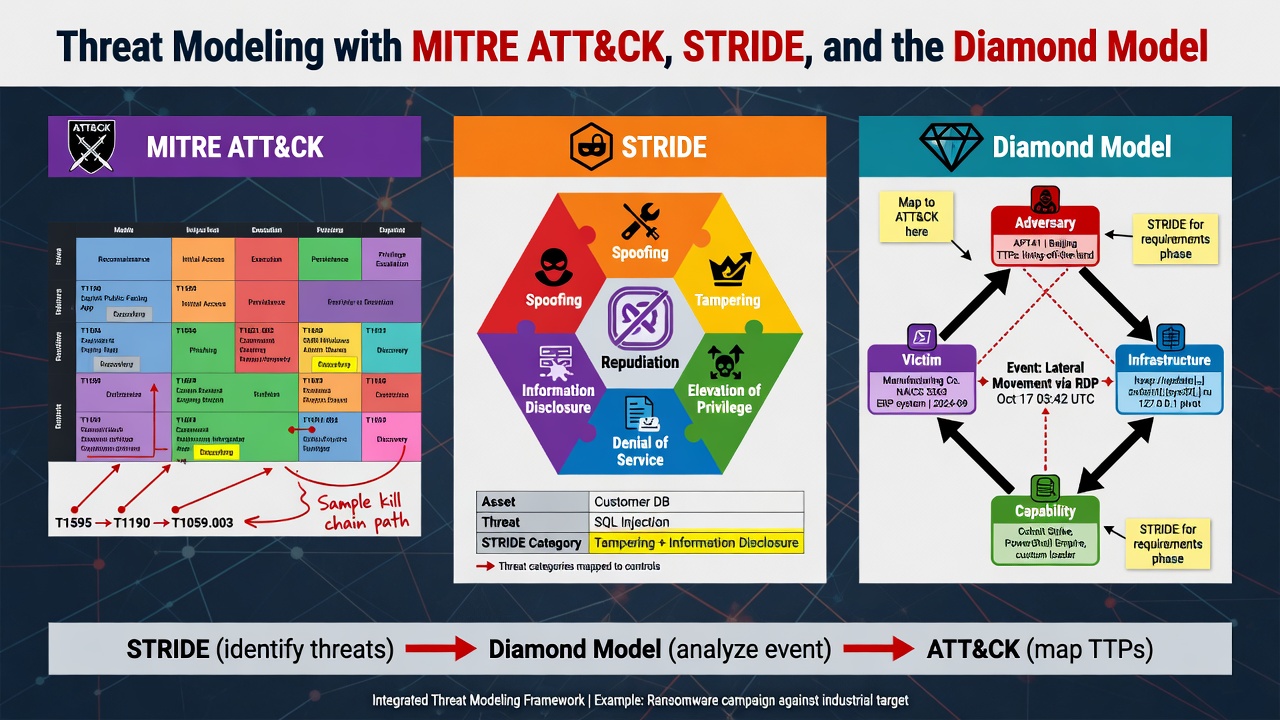
This guide shows how to combine MITRE ATT&CK, STRIDE, and the Diamond Model of Intrusion Analysis into a practical, exam-ready threat modeling workflow you can reuse for PBQs and real-world design reviews.[3][4][5]
TL;DR
Use MITRE ATT&CK to understand how adversaries operate, STRIDE to systematically enumerate what can go wrong in your design, and the Diamond Model to analyze who, why, and how incidents unfold over time.[3][4][5] For CAS-005, you’ll see these ideas in architecture PBQs, incident response scenarios, and risk-based control selection questions.[2]
1. Where Threat Modeling Fits in CAS-005
CompTIA CASP+ (CAS-005) emphasizes risk-driven security architecture and operations across on-premises, cloud, and hybrid environments.[1][2] The official objectives reference threat modeling, adversary tactics, kill chains, and security architecture decisions that balance business and technical constraints.[1][2]
Threat modeling in the CAS-005 context usually appears as:
- Design PBQs where you must choose or justify controls for a given architecture.
- Incident response or threat hunting scenarios that reference attacker behavior patterns.
- Risk management questions that ask you to prioritize mitigations based on impact and likelihood.[1][2]
Frameworks like MITRE ATT&CK, STRIDE, and the Diamond Model give you structured ways to think through these problems and defend your answers.[3][4][5]
2. Quick Overview of the Three Frameworks
Before we build a combined workflow, you need a crisp mental model of each framework.
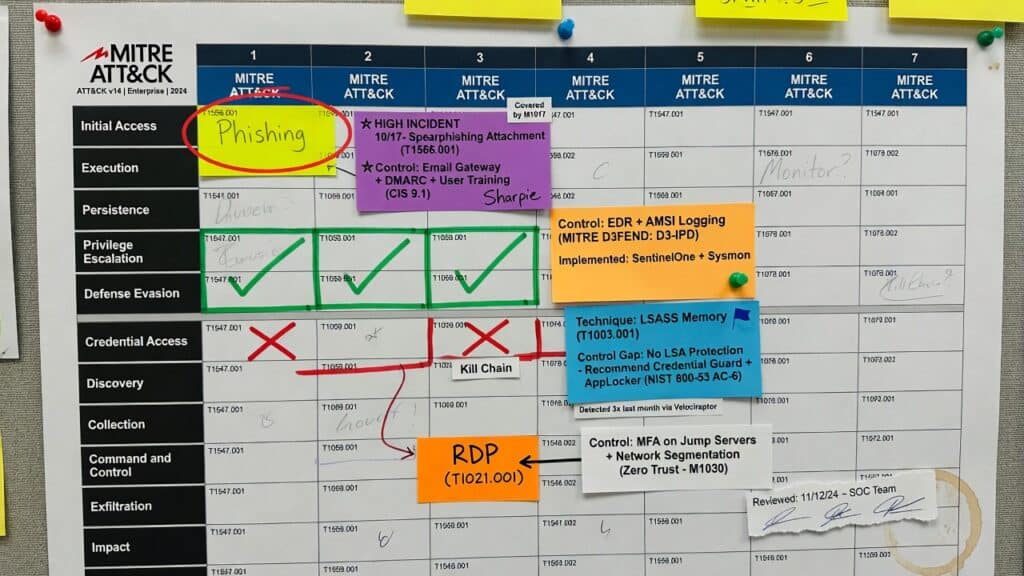
2.1 MITRE ATT&CK: Encyclopedia of Adversary Behavior
MITRE ATT&CK is a globally accessible knowledge base of adversary tactics, techniques, and procedures (TTPs) based on real-world observations.[3] It organizes behavior into matrices (Enterprise, Mobile, ICS) with columns representing tactics (goals, like Initial Access, Privilege Escalation) and rows representing techniques (how attackers achieve those goals).[3]
- Tactics = high-level objectives (e.g., Initial Access, Execution, Exfiltration).
- Techniques/Sub-techniques = concrete methods (e.g., Phishing, Command and Scripting Interpreter, Ingress Tool Transfer).[3]
- Each technique has example procedures, detection ideas, and mitigations.[3]
For CAS-005, ATT&CK helps you:
- Map attacker behavior to specific controls (e.g., EDR, application control, segmentation).[2][3]
- Support incident response playbooks and threat hunting hypotheses.[3]
- Explain “why this control here” in architecture and PBQ scenarios.[2][3]
2.2 STRIDE: Systematic Design-Time Threat Enumeration
STRIDE is a Microsoft-developed mnemonic for classifying application and system threats into six categories:[4]
- Spoofing identity
- Tampering with data
- Repudiation (denying actions)
- Information disclosure
- Denial of service
- Elevation of privilege[4]
STRIDE is usually applied to data flow diagrams (DFDs) or architecture diagrams: for each element (process, data store, external entity, data flow), you ask, “What STRIDE threats apply here?”[4]
For CAS-005, STRIDE is useful when you’re asked to:
- Review a proposed architecture and identify the most likely threat type.
- Choose mitigations for specific STRIDE categories (e.g., authentication for spoofing, integrity checks for tampering).[2][4]
- Explain how logging, non-repudiation, and access control reduce risk.[1][2][4]
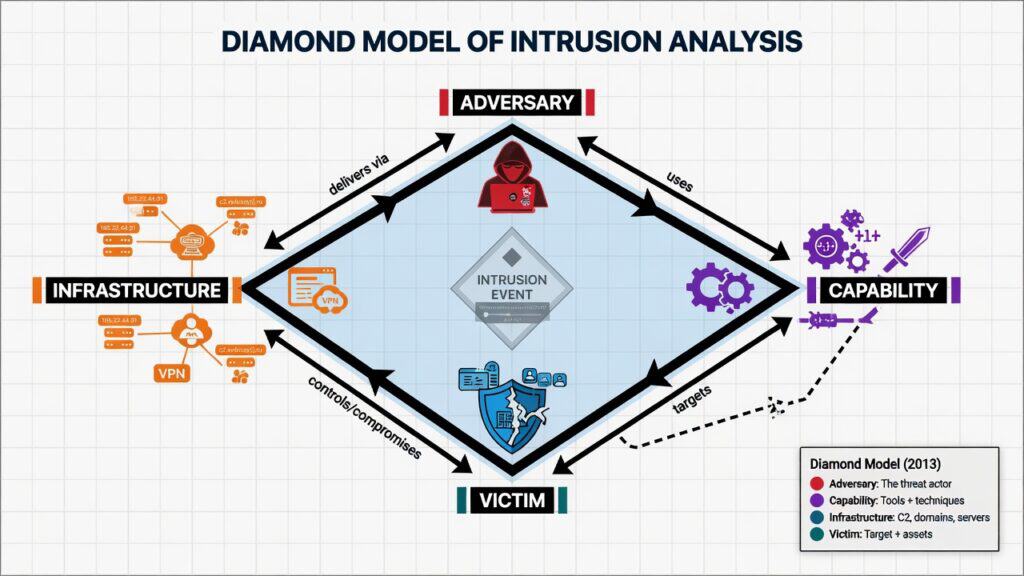
2.3 Diamond Model: Analyzing Intrusions as Connected Events
The Diamond Model of Intrusion Analysis describes each intrusion event as a relationship between four core features:[5]
- Adversary – the threat actor (individual, group, organization).
- Infrastructure – the systems and services used to deliver, control, or execute the attack (C2 servers, domains, cloud resources).
- Capability – tools, malware, exploits, and techniques the adversary uses.
- Victim – the target organization, system, or user.[5]
The model also includes meta-features such as timestamp, phase, result, and methodology, and defines axioms about how intrusions evolve over time.[5]
For CAS-005, the Diamond Model helps you:
- Think like a threat intelligence analyst when correlating events across logs and tools.[5]
- Identify opportunities to disrupt the adversary at different points (infrastructure takedown, tool detection, user training).[5]
- Explain kill chains and campaign analysis in incident response scenarios.[1][2][5]
3. When to Use Which Framework
In practice—and on CAS-005—you rarely use just one framework. Each shines at a different point in the lifecycle.
- STRIDE – best at design time for systematically thinking through what can go wrong in your architecture.[4]
- MITRE ATT&CK – best for operational and detection-focused modeling, mapping attacker behavior to controls and telemetry.[3]
- Diamond Model – best for incident and campaign analysis, tying together multiple events and understanding the adversary.[5]
For the exam, you should be able to:
- Identify which framework is most appropriate for a given scenario.
- Explain how you would combine them into a repeatable threat modeling workflow.[1][2]
4. Step-by-Step Threat Modeling Workflow (Combining All Three)
This section gives you a practical, repeatable workflow that aligns well with CAS-005 architecture and operations objectives.[1][2] You can adapt it to PBQs, tabletop exercises, or real system designs.
Step 1: Define the Scope, Assets, and Business Goals
Start with the basics: what system or workflow are you modeling, and why does it matter? CAS-005 expects you to tie security decisions to business objectives and risk appetite.[1][2]
- Identify critical assets (data, services, identities).
- Clarify business processes (e.g., customer portal login, payment processing).
- Note constraints (compliance, uptime SLAs, budget, legacy systems).[1][2]
On the exam, this often shows up as a paragraph of business context before the technical question. Don’t skip it—your threat model should reflect what the organization actually cares about.[1][2]
Step 2: Draw a Simple Data Flow / Architecture Diagram
You don’t need an art degree. CAS-005 cares that you understand trust boundaries, data flows, and dependencies, not that your diagram is pretty.[2]
- Identify external entities (users, third parties).
- Mark processes (web app, API gateway, auth service).
- Show data stores (databases, queues, object storage).
- Draw data flows and trust boundaries (internal vs external networks, cloud vs on-prem).[4]
This diagram becomes the substrate for STRIDE.
Step 3: Apply STRIDE to Each Element
Now walk each element and ask how the STRIDE categories apply.[4]
- Spoofing: Can an attacker pretend to be a user, service, or component? (Think: weak auth, missing mutual TLS.)
- Tampering: Can they alter data in transit or at rest? (Think: lack of integrity checks, insecure deserialization.)
- Repudiation: Could they deny actions due to missing logs or signatures?
- Information disclosure: Where might sensitive data leak?
- Denial of service: What could attackers flood, exhaust, or lock?
- Elevation of privilege: Are there paths to gain more access than intended?[4]
Capture threats in a simple table, for example:
Web app process – STRIDE example:
- Spoofing: Credential stuffing against login endpoint.
- Tampering: Manipulating JWT tokens if not signed/validated properly.
- Repudiation: Lack of audit logs for admin actions.
- Information disclosure: Verbose error messages exposing stack traces.
- Denial of service: Application-level DoS via expensive search queries.
- Elevation of privilege: Insecure direct object references (IDOR) in admin APIs.[4]
For CAS-005, you don’t have to label everything formally as STRIDE on the exam, but this mental checklist helps you avoid missing obvious issues.
Step 4: Layer in MITRE ATT&CK to Ground Threats in Real TTPs
Once you have a list of potential threats, use MITRE ATT&CK to make them concrete and map them to detection and mitigation options.[3]
- Identify relevant tactics (e.g., Initial Access, Persistence, Lateral Movement).[3]
- Pick representative techniques that match your STRIDE threats (e.g., phishing for spoofing, credential dumping for elevation of privilege).[3]
- Note ATT&CK’s suggested mitigations and detections for those techniques.[3]
Example mapping:
- Spoofing via credential stuffing → ATT&CK Credential Access tactics and techniques such as Brute Force and Valid Accounts → mitigations: MFA, strong password policies, anomaly detection.[3]
- Information disclosure via misconfigured S3 bucket → ATT&CK Exfiltration and Initial Access techniques → mitigations: least privilege IAM, configuration scanning, data classification.[3]
On CAS-005, using ATT&CK thinking helps you justify why a particular control or log source is the best answer among plausible options.[2][3]
Step 5: Use the Diamond Model to Think in Campaigns, Not Single Events
Now zoom out. The Diamond Model encourages you to see each event as part of a larger intrusion campaign with multiple linked diamonds over time.[5]
- Who is the adversary (or type of adversary)? What are their likely objectives?
- What infrastructure do they use (cloud accounts, domains, VPNs, residential proxies)?
- What capabilities (malware, tools, ATT&CK techniques) are in play?
- Who/what is the victim and what is the business impact?[5]
This perspective is especially useful for CAS-005 questions around:
- Threat intelligence program design.
- Incident response playbook development.
- Prioritizing mitigations that disrupt the adversary with minimal business impact.[1][2][5]
For example, if you know a particular threat group repeatedly reuses the same cloud provider and domain registration patterns, you can design controls and monitoring focused on that infrastructure—an insight that flows directly from the Diamond Model.[5]
Step 6: Prioritize and Select Controls
Finally, choose mitigations that balance risk reduction, cost, and usability—a core CAS-005 skill.[1][2]
- Use STRIDE to ensure you have coverage for all threat categories at critical components.
- Use ATT&CK to ensure controls map to real attacker techniques and can be monitored.[3]
- Use the Diamond Model to focus on controls that disrupt the adversary’s preferred infrastructure and capabilities.[5]
This is where exam questions often ask, “Which control provides the most effective mitigation for the described threat?” The best answer usually aligns with the dominant ATT&CK techniques and the business context described.[2][3]
5. Worked Example: CAS-005-Style Scenario
Let’s walk through a simplified scenario that mirrors CAS-005 exam style.
Scenario: You’re designing security for a customer-facing SaaS portal hosted in a public cloud. Users authenticate via SSO (OIDC), the app talks to microservices over an internal API gateway, and data is stored in a managed database and object storage. The organization has suffered credential stuffing attacks and a previous data exposure from a misconfigured storage bucket.[1][2]
Step A: STRIDE on Key Components
Consider three focal points: login endpoint, API gateway, and object storage.
- Login endpoint:
- Spoofing – credential stuffing, phishing against SSO.
- Repudiation – weak logging around login attempts.
- DoS – automated login attempts causing resource exhaustion.[4]
- API gateway:
- Tampering – manipulating JWTs or headers if not validated.
- Information disclosure – verbose error messages, weak access control on internal APIs.[4]
- Object storage:
- Information disclosure – public buckets, overly permissive IAM policies.
- Tampering – unauthorized modification of stored objects.[4]
Step B: Map to MITRE ATT&CK Techniques
Next, map these to representative ATT&CK techniques:[3]
- Credential stuffing → Brute Force and Valid Accounts under Credential Access.[3]
- Misconfigured object storage → Exfiltration via cloud storage under Exfiltration and Initial Access.[3]
- Manipulated tokens → Abuse of authentication tokens and web session hijacking techniques (Execution/Credential Access).[3]
From ATT&CK’s mitigations, you’d highlight:
- MFA and risk-based authentication for login.
- Rate limiting and anomaly detection on login endpoints.
- Least privilege IAM and configuration scanning for storage.
- Strong token signing, validation, and rotation for API security.[3]
Step C: Use the Diamond Model to Think Like an Adversary
Now frame the attack using the Diamond Model:[5]
- Adversary: financially motivated group targeting SaaS logins and data exfiltration.
- Infrastructure: botnets, credential stuffing tools, cloud-based proxies, throwaway email accounts.
- Capability: large credential dumps, automation frameworks, scripts targeting known SaaS APIs.
- Victim: your SaaS platform, specifically login and storage systems containing customer data.[5]
This lens suggests additional controls:
- Blocking or challenging traffic from known bad IP ranges or ASNs.
- Monitoring for unusual login patterns (geolocation, device fingerprinting).
- Threat intelligence feeds to detect reused infrastructure across campaigns.[5]
Step D: Prioritize Controls – Exam-Style Reasoning
In a CAS-005 question, you might be asked: “Which control most effectively reduces the risk of the described attacks while minimizing user friction?”
Given your threat model, the strongest primary answer is usually:
- Enforce adaptive MFA and implement credential stuffing protections at the identity provider and WAF/API gateway (mitigates spoofing and ATT&CK brute-force techniques).[2][3][4]
Secondary but still important answers might add:
- Automated configuration scanning and least-privilege IAM for storage.
- Centralized logging and analytics mapped to ATT&CK tactics.[1][3]
On the exam, think: “Which option best addresses the current stage of the attack, given the described techniques and business constraints?”
6. How CAS-005 Tests Threat Modeling Skills
CompTIA’s CAS-005 objectives include performance-based items and scenario-driven questions that require you to apply threat modeling concepts in context.[1][2] You won’t see “draw a STRIDE table” directly, but you will see its spirit.
6.1 Common Question Patterns
- Architecture review: Given a diagram and requirements, identify the most likely threat or the best control to add.
- Incident reconstruction: Given log snippets and indicators, sequence events and identify what the attacker is trying to do next (Diamond Model + ATT&CK).[1][3][5]
- Control justification: Choose between multiple controls and justify which better mitigates specific TTPs or STRIDE threats.[2][3][4]
6.2 What You Should Be Able to Do
- Explain, in plain language, when to use ATT&CK vs STRIDE vs the Diamond Model.
- Map a described attack to a sequence of ATT&CK tactics and techniques and propose detections.[3]
- Run a quick, mental STRIDE pass over a small architecture and identify missing controls.[4]
- Describe how threat intelligence and campaign analysis (Diamond Model) inform architecture and operations decisions.[1][2][5]
7. Practical Study Plan: Building Threat Modeling Muscle for CAS-005
To make this stick, you need practice—not just reading. Here’s a focused plan.
7.1 Week 1–2: Fundamentals and Vocabulary
- Read MITRE’s “Getting Started with ATT&CK” and browse the Enterprise matrix.[3]
- Review Microsoft’s STRIDE documentation and example threat models.[4]
- Skim the original Diamond Model paper’s introduction and core concepts.[5]
- Cross-reference CAS-005 objectives that mention threat modeling, adversary tactics, and incident analysis.[1][2]
7.2 Week 3–4: Apply to Two Real Systems
- Pick two systems you know well (e.g., VPN access, an internal web app, or an API).
- Draw a simple DFD and run a STRIDE pass for each.[4]
- Identify 5–10 relevant ATT&CK techniques and explicit mitigations.[3]
- Write a short Diamond Model-style intrusion story for each system (who, what, how, why, and impact).[5]
7.3 Week 5+: Practice Exam-Style Reasoning
- Take CAS-005 practice questions and rewrite the scenario as a mini threat model.
- For each wrong answer, ask, “Which STRIDE threat or ATT&CK technique did I overlook?”
- For IR scenarios, sketch a quick Diamond Model to see what you missed.[1][2][3][5]
Integrate this with broader CAS-005 prep around zero trust, cloud security, and incident response.[1][2][3] For example, when you study zero trust, explicitly map controls to ATT&CK techniques and STRIDE threats on your high-value assets.
8. Key Takeaways for the CAS-005 Exam and Your Day Job
Threat modeling with MITRE ATT&CK, STRIDE, and the Diamond Model is not academic theory—it’s how senior practitioners and exam writers structure their thinking.[1][2][3][4][5]
- Use STRIDE to systematically find design flaws and missing controls in architectures.[4]
- Use MITRE ATT&CK to ground threats in real TTPs and choose effective detections and mitigations.[3]
- Use the Diamond Model to understand intrusions over time and design defenses that disrupt entire campaigns.[5]
- For CAS-005, practice applying all three in time-limited, scenario-driven questions.[1][2]
If you can explain your architecture and incident response decisions using these frameworks, you’ll be in a strong position both for the CAS-005 exam and for leading threat modeling sessions in your organization.[1][2][3][4][5]
Bibliography
- CompTIA. (2023). CompTIA CASP+ (CAS-005) certification exam objectives [Certification exam objectives]. CompTIA. https://www.comptia.org/certifications/casp
- CompTIA. (n.d.). CompTIA CASP+ certification. CompTIA. https://www.comptia.org/certifications/casp
- MITRE Corporation. (2019). Getting started with ATT&CK (Rev. 1.0) [White paper]. MITRE. https://attack.mitre.org/resources/
- Microsoft. (n.d.). Microsoft threat modeling tool and STRIDE model [Documentation]. Microsoft Learn. https://learn.microsoft.com/en-us/azure/security/develop/threat-modeling-tool-threats
- Caltagirone, S., Pendergast, A., & Betz, C. (2013). The Diamond Model of Intrusion Analysis [Technical report]. Center for Cyber Intelligence Analysis and Threat Research. https://apps.dtic.mil/sti/citations/ADA586960